Have you heard that a Google security researcher discovered a 20-year-old unpatched vulnerability in all versions of Windows? Read this post to know the details about this vulnerability. Then, you can update your computer to fix this problem. With MiniTool Partition Wizard, you can rescue your data from virus attack.
The 20-Year-Old Unpatched Vulnerability
Last month, a Google security researcher revealed details of a 20-year-old unpatched high-severity vulnerability, which affects all versions of Microsoft Windows, back from Windows XP to the latest Windows 10. It was very possible that someone may reach across sessions and violate NT security boundaries for nearly twenty years, and nobody noticed.
This vulnerability exists in the communication way between MSCTF clients and server, allowing even a low privileged or a sandboxed application to read and write data to a higher privileged application.
What’s MSCTF? It is a module in Text Services Framework (TSF) of the Windows operating system that manages things like input methods, keyboard layouts, text processing, and speech recognition.
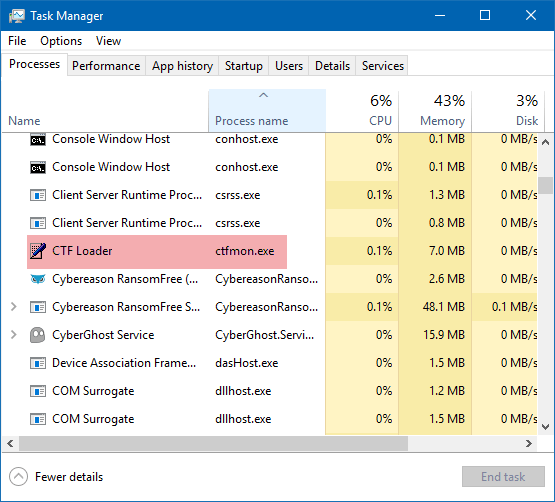
When you log into your Windows machine, it starts a CTF monitor service. Then, the Windows kernel forces applications to connect to the CTF monitor service when they start.
The CTF monitor service is responsible for notifying applications about changes in keyboard layout or input methods, and works as a central manager to handle communications between all clients through an ALPC (advanced local procedure call) port. Please note that a client is a window for each process running on the same session.
The Specific Harms
Since there is no access control or any kind of authentication set in the interaction between MSCTF clients and server, an attacker could connect to another user’s active session and take over any application, or wait for an Administrator to login and compromise their session.
This weakness in CTF protocol could allow any application, any user, and even sandboxed processes to:
- connect to CTF monitor ALPC port across all sessions;
- read and write the text of any window, from any other session;
- fake their thread id, process ID, and HWND;
- pretend as a CTF service, tricking other applications, even privileged ones, to connect to it;
- escape from sandboxes and escalate privileges.
In addition, with this weakness, attackers can easily bypass User Interface Privilege Isolation (UIPI), allowing even an unprivileged process to:
- read sensitive text from any window of other applications, including passwords out of dialog boxes;
- gain SYSTEM privileges;
- take control of the UAC consent dialog;
- send commands to the administrator’s console session;
- escape IL/AppContainer sandboxes by sending input to unsandboxed windows.
An attacker who successfully exploited this vulnerability could run arbitrary code in the security context of the local system. He could then install programs; view, change, or delete data; or create new accounts with full user rights.
Besides this vulnerability, it is reported that CTF protocol also contains many memory corruption flaws that can be exploited in a default configuration. The researcher has also released a custom open-source “CTF Exploration Tool” on Github that is developed and used to discover many critical security issues in the Windows CTF protocol.
Finally, the researcher reported his findings to Microsoft in mid-May this year and released the details to the public after Microsoft failed to address the issue within 90 days of being notified.
On August 13, Microsoft has finally released an update to address this vulnerability, tracked as CVE-2019-1162, by correcting how Windows handles calls to ALPC.



User Comments :