Have you heard of PXJ ransomware? This ransomware has emerged in the wild in early 2020 and is identified by X-Force IRIS. In this post, MiniTool introduces PXJ ransomware in detail and offers some advice on dealing with this ransomeware.
What Is PXJ Ransomware?
According to the FBI, cybercrime losses have tripled in the last five years and ransomware has become one of the most profitable types of malware in the hands of cybercriminals. Recently, IBM’s X-Force Incident Response and Intelligence Services (IRIS) discovered activity related to a new strain of ransomware, which is known as “PXJ” or “XVFXGW”.
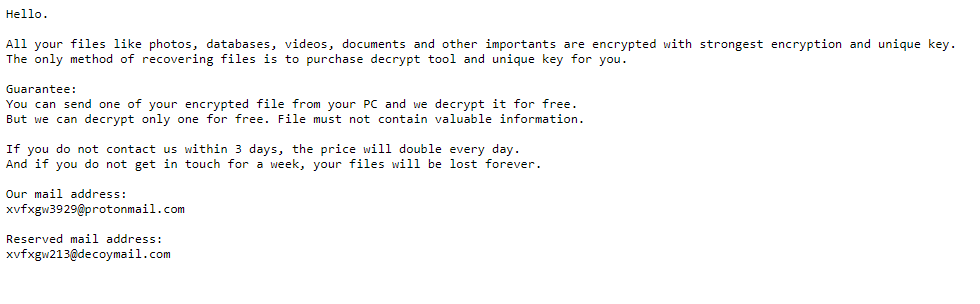
The name PXJ is derived from the file extension that is appended to encrypted files, while the name XVFXGW is based on both the mutex the malware creates, “XVFXGW DOUBLE SET,” and the email addresses listed in the ransom note, which are “[email protected]” and “[email protected].”
This ransomware performs functions common to most ransomware, but it does not appear to share underlying code with known ransomware families. It behaves as follows:
Step 1: Use the “SHEmptyRecycleBinW” function to empty the Recycle Bin.
Step 2: Execute specific commands to prevent the recovery of data after it has been encrypted. The steps taken at this stage include the deletion of volume shadow copies and the disabling of the Windows Error Recovery service.
Step 3: Use both AES and RSA algorithms to lock down data, including photos and images, databases, documents, videos and other files on the device. In this way, it can prevent potential recovery by breaking the encryption.
Note: AES algorithm can help ransomware to encrypt files faster so that the malicious process can’t be interrupted before it’s finished. Then, the AES key is encrypted with the stronger asymmetric key—RSA.
Step 4: With encryption complete, the ransom note is dropped as a file named “LOOK.txt” and requests that the user contact the operator via email to pay the ransom in exchange for the decryption key.
The attacker threatens victims that if they do not pay immediately, the ransom amount will double every day after the first three days and if they do not contact Pxj’s developers within one week, the decryption key will supposedly be destroyed, leaving the encrypted files unrecoverable forever.
Your Computer Has Been Locked? Ransomware Prevention Policy, Protect Yourself Now!
How to Deal with PXJ Ransomware?
If you have not installed PXJ Ransomware, yet, you should take measures to avoid that. For example, ignore the attachments of spam mail file which received through unknown address, scan the System with reputable antimalware tool, etc.
If you have encountered PXJ Ransomware, you can try the following steps to restore your computer and files:
Step 1: Hold down “Shift” key while you are clicking Power> Restart button. In this way, you can enter WinRE.
Step 2: Navigate to Troubleshoot > Advanced options > System Restore. Follow the wizard to restore your computer to a point where your PC is not infected with PXJ Ransomware.
Step 3: After System Restore is completed, open the browser and download a legitimate anti-malware tool. Do a full system scanning to remove all the malicious detected entries.
Step 4: Right click encrypted files and go to Properties > Previous Version tab. Select a Restore Point and click on Restore option.
If the above steps can’t help you access the encrypted files, you can use a data recovery tool like MIniTool Partition Wizard to help you recover data. Click How To Recover Files Deleted By Virus Attack to get detailed steps.

User Comments :